History
In 1979, network time synchronization technology was used in what was possibly the first public demonstration of Internet services running over a trans-Atlantic satellite network, at the National Computer Conference in New York. The technology was later described in the 1981 Internet Engineering Note (IEN) 173[6] and a public protocol was developed from it that was documented in RFC 778. The technology was first deployed in a local area network as part of the Hello routing protocol and implemented in the Fuzzball router, an experimental operating system used in network prototyping, where it ran for many years.
Other related network tools were available both then and now. They include the Daytime and Time protocols for recording the time of events, as well as the ICMP Timestamp and IP Timestamp option (RFC 781). More complete synchronization systems, although lacking NTP's data analysis and clock disciplining algorithms, include the Unix daemon timed, which uses an election algorithm to appoint a server for all the clients;[7] and the Digital Time Synchronization Service (DTSS), which uses a hierarchy of servers similar to the NTP stratum model.
In 1985, NTP version 0 (NTPv0) was implemented in both Fuzzball and Unix, and the NTP packet header and round-trip delay and offset calculations, which have persisted into NTPv4, were documented in RFC 958. Despite the relatively slow computers and networks available at the time, accuracy of better than 100 milliseconds was usually obtained on Atlantic spanning links, with accuracy of tens of milliseconds on Ethernet networks.
In 1988, a much more complete specification of the NTPv1 protocol, with associated algorithms, was published in RFC 1059. It drew on the experimental results and clock filter algorithm documented in RFC 956 and was the first version to describe the client-server and peer-to-peer modes. In 1991, the NTPv1 architecture, protocol and algorithms were brought to the attention of a wider engineering community with the publication of an article by David L. Mills in the IEEE Transactions on Communications.[8]
In 1989, RFC 1119 was published defining NTPv2 by means of a state machine, with pseudocode to describe its operation. It introduced a management protocol and cryptographic authentication scheme which have both survived into NTPv4. The design of NTPv2 was criticized for lacking formal correctness principles by the DTSS community. Their alternative design included Marzullo's algorithm, a modified version of which was promptly added to NTP.[citation needed] The bulk of the algorithms from this era have also largely survived into NTPv4.
In 1992, RFC 1305 defined NTPv3. The RFC included an analysis of all sources of error, from the reference clock down to the final client, which enabled the calculation of a metric that helps choose the best server where several candidates appear to disagree. Broadcast mode was introduced.
In subsequent years, as new features were added and algorithm improvements were made, it became apparent that a new protocol version was required.[9] In 2010, RFC 5905 was published containing a proposed specification for NTPv4. The protocol has significantly moved on since then, and as of 2014, an updated RFC has yet to be published.[10] Following the retirement of Mills from the University of Delaware, the reference implementation is currently maintained as an open source project led by Harlan Stenn.[11][12]
Clock strata
NTP uses a hierarchical, semi-layered system of time sources. Each level of this hierarchy is termed a stratum and is assigned a number starting with zero for the reference clock at the top. A server synchronized to a stratum n server runs at stratum n + 1. The number represents the distance from the reference clock and is used to prevent cyclical dependencies in the hierarchy. Stratum is not always an indication of quality or reliability; it is common to find stratum 3 time sources that are higher quality than other stratum 2 time sources.[note 1] A brief description of strata 0, 1, 2 and 3 is provided below.
- Stratum 0
- These are high-precision timekeeping devices such as atomic clocks, GPS or other radio clocks. They generate a very accurate pulse per second signal that triggers an interrupt and timestamp on a connected computer. Stratum 0 devices are also known as reference clocks.
- Stratum 1
- These are computers whose system time is synchronized to within a few microseconds of their attached stratum 0 devices. Stratum 1 servers may peer with other stratum 1 servers for sanity check and backup.[13] They are also referred to as primary time servers.[2][3]
- Stratum 2
- These are computers that are synchronized over a network to stratum 1 servers. Often a stratum 2 computer will query several stratum 1 servers. Stratum 2 computers may also peer with other stratum 2 computers to provide more stable and robust time for all devices in the peer group.
- Stratum 3
- These are computers that are synchronized to stratum 2 servers. They employ the same algorithms for peering and data sampling as stratum 2, and can themselves act as servers for stratum 4 computers, and so on.
The upper limit for stratum is 15; stratum 16 is used to indicate that a device is unsynchronized. The NTP algorithms on each computer interact to construct a Bellman-Ford shortest-path spanning tree, to minimize the accumulated round-trip delay to the stratum 1 servers for all the clients.[1]:20
Timestamps
The 64-bit timestamps used by NTP consist of a 32-bit part for seconds and a 32-bit part for fractional second, giving a time scale that rolls over every 232 seconds (136 years) and a theoretical resolution of 2−32 seconds (233 picoseconds). NTP uses an epoch of January 1, 1900 so the first rollover will be on February 7, 2036.[14][15]
Future versions of NTP may extend the time representation to 128 bits: 64 bits for the second and 64 bits for the fractional-second. The current NTPv4 format has support for Era Number and Era Offset, that when used properly should aid fixing date rollover issues. According to Mills, "the 64 bit value for the fraction is enough to resolve the amount of time it takes a photon to pass an electron at the speed of light. The 64 bit second value is enough to provide unambiguous time representation until the universe goes dim."[16][note 2]
Clock synchronization algorithm
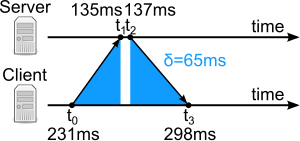
A typical NTP client will regularly poll three or more servers on diverse networks. To synchronize its clock, the client must compute their time offset and round-trip delay. Time offset θ is defined by
- ,
and the round-trip delay δ by
- ,
where
- t0 is the client's timestamp of the request packet transmission,
- t1 is the server's timestamp of the request packet reception,
- t2 is the server's timestamp of the response packet transmission and
- t3 is the client's timestamp of the response packet reception.[1]:19
The values for θ and δ are passed through filters and subjected to statistical analysis. Outliers are discarded and an estimate of time offset is derived from the best three remaining candidates. The clock frequency is then adjusted to reduce the offset gradually, creating a feedback loop.[1]:20
The synchronization is correct when both the incoming and outgoing routes between the client and the server have symmetrical nominal delay. If the routes do not have a common nominal delay, there will be a systematic bias of half the difference between the forward and backward travel times.[17]
Software implementations
Reference implementation
The NTP reference implementation, along with the protocol, has been continuously developed for over 20 years. Backwards compatibility has been maintained as new features have been added. It contains several sensitive algorithms, especially to discipline the clock, that can misbehave when synchronized to servers that use different algorithms. The software has been ported to almost every computing platform, including personal computers.[1]:13 It runs as a daemon called ntpd under Unix or as a service under Windows.[1]:15 Reference clocks are supported and their offsets are filtered and analysed in the same way as remote servers, although they are usually polled more frequently.[1]:19
| Reference indentifier (refid) | Clock Source |
|---|---|
| GOES | Geosynchronous Orbit Environment Satellite |
| GPS | Global Positioning System |
| GAL | Galileo Positioning System |
| PPS | Generic pulse-per-second |
| IRIG | Inter-Range Instrumentation Group |
| WWVB | LF Radio WWVB Ft. Collins, CO 60 kHz |
| DCF | LF Radio DCF77 Mainflingen, DE 77.5 kHz |
| HBG | LF Radio HBG Prangins, HB 75 kHz (ceased operation) |
| MSF | LF Radio MSF Anthorn, UK 60 kHz |
| JJY | LF Radio JJY Fukushima, JP 40 kHz, Saga, JP 60 kHz |
| LORC | MF Radio LORAN C station, 100 |
| TDF | MF Radio Allouis, FR 162 kHz |
| CHU | HF Radio CHU Ottawa, Ontario |
| WWV | HF Radio WWV Ft. Collins, CO |
| WWVH | HF Radio WWVH Kauai, HI |
| NIST | NIST telephone modem |
| ACTS | NIST telephone modem |
| USNO | USNO telephone modem |
| PTB | European telephone modem |
| MRS | Multi Reference Sources |
| XFAC | Inter Face Association Change |
The table shows common time reference indentifiers (refid) codes. Other refid codes can be defined and encountered.
SNTP
A less complex implementation of NTP, using the same protocol but without requiring the storage of state over extended periods of time,[18] is known as the Simple Network Time Protocol (SNTP). It is used in some embedded devices and in applications where full NTP capability is not required.[19]
Windows Time service
All Microsoft Windows versions since Windows 2000 include the Windows Time service ("W32Time"),[20] which has the ability to synchronize the computer clock to an NTP server.
The W32Time service was originally implemented for the purpose of the Kerberos version 5 authentication protocol, which required time to be within 5 minutes of the correct value to prevent replay attacks. The version in Windows 2000 and Windows XP only implements SNTP, and violates several aspects of the NTP version 3 standard.[21] Beginning with Windows Server 2003 and Windows Vista, a compliant implementation of full NTP is included.[22] Microsoft says that the W32Time service cannot reliably maintain sync time to the range of 1 to 2 seconds.[23] If higher accuracy is desired, Microsoft recommends using a different NTP implementation.[24]
Windows Server 2016 now supports 1 ms time accuracy under certain operating conditions.[25]
OpenNTPD
In 2004, Henning Brauer presented OpenNTPD, an NTP implementation with a focus on security and encompassing a privilege separated design. Whilst it is aimed more closely at the simpler generic needs of OpenBSD users, it also includes some protocol security improvements whilst still being compatible with existing NTP servers. It was originally designed for OpenBSD but has a portable version available and that has been made available as a package in Linux package repositories.
Ntimed
A new NTP client, ntimed, was started by Poul-Henning Kamp in 2014.[26] The new implementation is sponsored by the Linux Foundation as a replacement for the reference implementation, as it was determined to be easier to write a new implementation from scratch than to fix the existing issues with the large existing code base. As of June 2015, no official release was done yet, but ntimed can synchronize clocks reliably.[27]ntimed works under Debian and FreeBSD, but remains to be ported to Windows and macOS.[28]
NTPsec
NTPsec is a fork of the reference implementation that has been systematically security-hardened. The fork point was in June 2015 and was in response to a rash of compromises in 2014; as of 2017, the software is in beta testing.[29] Between removal of unsafe features, removal of support for obsolete hardware, and removal of support for obsolete Unix variants, NTPsec has been able to pare away 60% of the original codebase, making the remainder more auditable.[30]
Chrony
Chrony comes by default in Red Hat distributions[31] and is available in the Ubuntu repositories[32]. Chrony is aimed at ordinary computers, which are unstable, go into sleep mode or have intermittent connection to the Internet. Chrony is also designed for virtual machines, a much more unstable environment. It is characterized by low resource consumption (cost) and supports PTP as well as NTP. It has two main components: chronyd a daemon that is executed when the computer starts and chronyc a command line interface to the user for its configuration. It has been evaluated as very safe and with just a few incidents[33], its advantage is the versatility of its code, written from scratch to avoid the complexity of code[34]. Chrony is written under GNU General Public License version 2, was created by Richard Curnow in 1997 with others along time and is currently maintained by Miroslav Lichvar, development supported by Red Hat Software [35].
Leap seconds
On the day of a leap second event, ntpd receives notification from either a configuration file, an attached reference clock, or a remote server. Because of the requirement that time must appear to be monotonically increasing, a leap second is inserted with the sequence 23:59:59, 23:59:60, 00:00:00. Although the clock is actually halted during the event, any processes that query the system time cause it to increase by a tiny amount, preserving the order of events. If a negative leap second should ever become necessary, it would be deleted with the sequence 23:59:58, 00:00:00, skipping 23:59:59.[36]
Security concerns
Several security concerns arose in late 2014. Previously, researchers became aware that NTP servers can be susceptible to man-in-the-middle attacks unless packets are cryptographically signed for authentication.[37] The computational overhead involved can make this impractical on busy servers, particularly during denial of service attacks.[38] NTP message spoofing can be used to move clocks on client computers and allow a number of attacks based on bypassing of cryptographic key expiration.[39] Some of the services affected by fake NTP messages identified are TLS, DNSSEC, various caching schemes (such as DNS cache), BGP, Bitcoin and a number of persistent login schemes.[40][41]
Only a few other security problems have been identified in the reference implementation of the NTP codebase in its 25+ year history, but the ones that have appeared recently are cause for significant concern.[42][43] The protocol has been undergoing revision and review over its entire history. As of January 2011, there are no security revisions in the NTP specification and no reports at CERT.[44] The current codebase for the reference implementation has been undergoing security audits from several sources for several years now, and there are no known high-risk vulnerabilities in the current released software.[45]
Several NTP server misuse and abuse practices exist which cause damage or degradation to a Network Time Protocol (NTP) server.
NTP has been used in distributed denial of service (DDoS) attacks.[46][47] A small query is sent to an NTP server with the return address spoofed to be the target address. Similar to the DNS amplification attack, the server responds with a much larger reply that allows an attacker to substantially increase the amount of data being sent to the target. To avoid participating in an attack, servers can be configured to ignore external queries, or they can be upgraded to version 4.2.7p26 or later.[48]
A stack-based buffer overflow exploit was discovered and a patch is available as of December 19, 2014. This includes all NTP Version 4 releases before version 4.2.8.[49]Apple was concerned enough that it used its auto-update capability for the first time,[50] though only for recent versions of macOS. In the case of version 10.6.8 there are manual fixes for the server version, and normal "client" users can just turn off automatic time updating in System Preferences for Date & Time.[51] Researchers[which?] believe that the protocol design is excellent and that the flaws are appearing in implementations of the protocol. Some errors are basic, such as a missing return statement in a routine, that can lead to unlimited access to systems that are running some versions of NTP in the root daemon. Systems that do not use the root daemon, such as BSD, are not subject to this flaw.[52]
See also
- Allan variance
- Clock network
- International Atomic Time
- NIST
- NITZ
- NTP pool
- NTP server misuse and abuse
- Ntpdate
- OpenNTPD
- Precision Time Protocol (IEEE 1588 PTP)
Notes
- Telecommunication systems use a different definition for clock strata.
- 2−64 seconds is about 54 zeptoseconds (light would travel 16.26 picometers, or approximately 0.31 × Bohr radius), and 264 seconds is about 585 billion years.
References
- David L. Mills (12 December 2010). Computer Network Time Synchronization: The Network Time Protocol. Taylor & Francis. pp. 12–. ISBN 978-0-8493-5805-0.
- "Executive Summary: Computer Network Time Synchronization". Retrieved 2011-11-21.
- "NTP FAQ". The NTP Project. Retrieved 2011-08-27.
- "Port Numbers". The Internet Assigned Numbers Authority (IANA).
- Page 16
- D.L. Mills (25 February 1981), Time Synchronization in DCNET Hosts, archived from the original on 1996-12-30
- "TIMED(8)", UNIX System Manager's Manual, retrieved 2017-09-12
- David L. Mills (October 1991). "Intern Time Synchronization: The Network Time Protocol" (PDF). IEEE Transactions on Communications. IEEE. 39 (10). doi:10.1109/26.103043.
- David L. Mills (15 November 2010). Computer Network Time Synchronization: The Network Time Protocol on Earth and in Space, Second Edition. CRC Press. p. 377. ISBN 978-1-4398-1464-2.
- "Future Plans", Network Time Synchronization Research Project, retrieved 24 December 2014
- "NTP Needs Money: Is A Foundation The Answer?". InformationWeek. March 23, 2015. Retrieved April 4, 2015.
- "NTP's Fate Hinges On 'Father Time'". InformationWeek. March 11, 2015. Retrieved April 4, 2015.
- "Network Time Protocol: Best Practices White Paper". Retrieved 15 October 2013.
- David L. Mills (12 May 2012). "The NTP Era and Era Numbering". Retrieved 24 September 2016.
- W. Richard Stevens; Bill Fenner; Andrew M. Rudoff (2004). UNIX Network Programming. Addison-Wesley Professional. pp. 582–. ISBN 978-0-13-141155-5.
- University of Delaware Digital Systems Seminar presentation by David Mills, 2006-04-26
- Gotoh, T.; Imamura, K.; Kaneko, A. (2002). Improvement of NTP time offset under the asymmetric network with double packets method. Conference on Precision Electromagnetic Measurements. pp. 448–449. doi:10.1109/CPEM.2002.1034915. ISBN 0-7803-7242-5.
- "Network Time Protocol Version 4: Protocol and Algorithms Specification". June 2010. p. 54. Retrieved 2012-08-26.
Primary servers and clients complying with a subset of NTP, called the Simple Network Time Protocol (SNTPv4) [...], do not need to implement the mitigation algorithms [...] The fully developed NTPv4 implementation is intended for [...] servers with multiple upstream servers and multiple downstream servers [...] Other than these considerations, NTP and SNTP servers and clients are completely interoperable and can be intermixed [...]
- Simple Network Time Protocol (SNTP) Version 4 for IPv4, IPv6 and OSI. doi:10.17487/RFC4330. RFC 4330.
- "Windows Time Service Technical Reference". technet.microsoft.com. 2011-08-17. Retrieved 2011-09-19.
- "Windows Time Service page at NTP.org". Support.ntp.org. 2008-02-25. Retrieved 2011-01-12.
- "How the Windows Time Service Works". technet.microsoft.com. 2010-03-12. Retrieved 2011-09-19.
- "Support boundary to configure the Windows Time service for high accuracy environments". Microsoft Corporation. 2011-10-19.
- Ned Pyle (2007-10-23). "High Accuracy W32time Requirements". Microsoft Corporation. Retrieved 2012-08-26.
- "Windows Server 2016 Accurate Time". technet.microsoft.com.
- Poul-Henning, Kamp. "20140926 – Playing with time again". PHK's Bikeshed. Retrieved 4 June 2015.
- Poul-Henning, Kamp. "Network time synchronization software, NTPD replacement". ntimed git repository README file. Github. Retrieved 4 June 2015.
- Poul-Henning, Kamp (2015-01-11). "20150111 – What happened next?". PHK's Bikeshed. Retrieved 4 June 2015.
- "The Secure Network Time Protocol (NTPsec) Distribution". Retrieved 2017-08-28.
- Allan Liska (December 10, 2016). NTP Security: A Quick-Start Guide. Apress. pp. 80–. ISBN 978-1-4842-2412-0.
- Lichvar, Miroslav (20 July 2016). "Combining PTP with NTP to Get the Best of Both Worlds". Red Hat Enterprise Linux Blog. Red Hat. Archived from the original on 30 July 2016. Retrieved 19 November 2017.
Starting with Red Hat Enterprise Linux 7.0 (and now in Red Hat Enterprise Linux 6.8) a more versatile NTP implementation is also provided via the chrony package
- Lichtenheld, Frank. "Package: chrony (2.1.1-1) [universe]". Ubuntu Package. Ubuntu Package. Archived from the original on 19 November 2017. Retrieved 19 November 2017.
Versatile implementation of the Network Time Protocol
- Heiderich, Mario (August 2017). "Pentest-Report Chrony 08.2017" (PDF). Cure53.de Team. wiki.mozilla.org, AKA MozillaWiki or WikiMO. Archived from the original (pdf) on 5 October 2017. Retrieved 19 November 2017.
Withstanding eleven full days of on-remote testing in August of 2017 means that Chrony is robust, strong, and developed with security in mind.
- "Securing Network Time". Core Infrastructure Initiative, a Linux Foundation Collaborative Project. Core Infrastructure Initiative. 27 September 2017. Archived from the original on 28 October 2017. Retrieved 19 November 2017.
In sum, the Chrony NTP software stands solid and can be seen as trustworthy
- "chrony introduction". TuxFamily, a non-profit organization. chrony. Archived from the original on 9 December 2009. Retrieved 19 November 2017.
The software is supported on Linux, FreeBSD, NetBSD, macOS, and Solaris.
- David Mills. "The NTP Timescale and Leap Seconds". Retrieved 15 October 2013.
- "Network Time Protocol Version 4: Autokey Specification". IETF. 2010. Retrieved 2014-10-16.
- "NTP Security Analysis". Retrieved 11 October 2013.
- Jose Selvi (2014-10-16). "Bypassing HTTP Strict Transport Security" (PDF). Retrieved 2014-10-16.
- Aanchal Malhotra; Isaac E. Cohen; Erik Brakke & Sharon Goldberg (20 October 2015). "Attacking the Network Time Protocol" (PDF). NDSS.
- "Attacking the Network Time Protocol". www.cs.bu.edu. Retrieved 2015-10-27.
- "Security Notice". Support.ntp.org. 2009-12-10. Retrieved 2011-01-12.
- results returned by a search on "Network Time Protocol"[permanent dead link] at [1][original research?]
- in RFC 778, RFC 891, RFC 956, RFC 958, RFC 1305, RFC 5905, and the NTPv4 specification
- "Code Audit". Support.ntp.org. 2009-06-13. Retrieved 2011-01-12.
- Goodin, Dan (2014-01-13). "New DoS attacks taking down game sites deliver crippling 100Gbps floods". Ars Technica. Retrieved 2014-01-25.
- Lee, Dave (2014-02-11). "Huge hack 'ugly sign of future' for internet threats". BBC. Retrieved 2014-02-12.
- "DRDoS / Amplification Attack using ntpdc monlist command". support.ntp.org. 2010-04-24. Retrieved 2014-04-13.
- "Network Time Protocol Vulnerabilities (Update C) | ICS-CERT". Ics-cert.us-cert.gov. Retrieved 2015-04-15.
- Cunningham, Andrew (Dec 23, 2014). "Apple automatically patches Macs to fix severe NTP security flaw". arstechnica. Retrieved Apr 29, 2015.
- "NTP vulnerability on versions prior to 4.2.8 -- we OK?". Apple Support Communities.
- Fairhead, Harry (23 December 2014). "NTP The Latest Open Source Security Problem". I Programmer.
Further reading
- Definitions of Managed Objects for Network Time Protocol Version 4 (NTPv4). doi:10.17487/RFC5907. RFC 5907.
- Network Time Protocol (NTP) Server Option for DHCPv6. doi:10.17487/RFC5908. RFC 5908.
External links
- Log in to post comments